Our Services

Our hacker-led methodology puts us in the mindset of real-world attackers allowing us to simulate genuine threat scenarios and expose weaknesses that traditional security assessments often miss.
Every engagement is executed by highly specialized security professionals who combine deep technical expertise with a nuanced understanding of business impact and risk prioritization. This ensures that our findings go beyond technical details-providing clear, actionable insights that help organizations strengthen their defenses, improve resilience, and make informed security investments.
Whether it’s a one-time penetration test, an adversarial simulation, or a full red team exercise, Beetles partners with you to transform vulnerabilities into opportunities for growth and maturity in your cybersecurity posture.
Each service is delivered by our team of specialized security professionals who combine technical expertise with a deep understanding of business risk to provide actionable security insights.




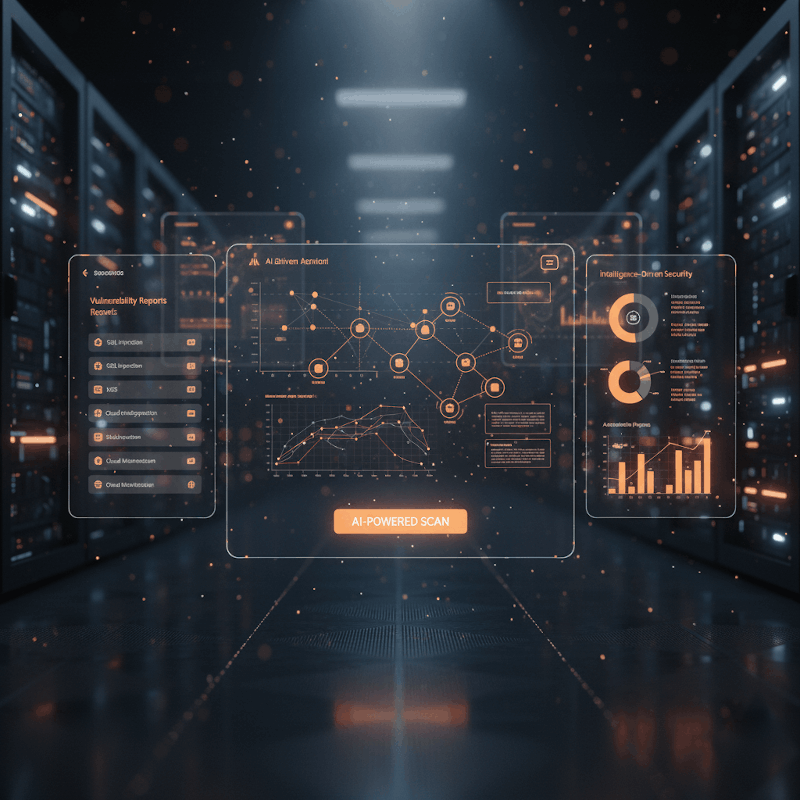
AI-Powered PenTesting
Our custom AI-driven PenTesting process combines human expertise with our proprietary Large Language Models to accelerate discovery, analysis, and reporting of vulnerabilities. It continuously learns from attack patterns to deliver faster, smarter, and more adaptive testing.
- Automated reconnaissance and threat modeling
- AI-assisted exploit path generation
- Real-time risk correlation and prioritization
- Adaptive remediation recommendations
- Continuous learning from previous engagementss
Web Application PenTesting
Our web application PenTesting service identifies security vulnerabilities in your web applications that automated scanners miss. We follow OWASP Top 10 and ASVS frameworks to provide comprehensive coverage of potential attack vectors.
- Manual testing by experienced ethical hackerst
- Identification of business logic flaws
- Authentication and authorization bypass testing
- Session management assessment
- Input validation and sanitization checks

Mobile Application Security Testing
Mobile applications often handle sensitive user data and require specialized security testing. Our mobile application security testing service identifies vulnerabilities in both Android and iOS applications through static and dynamic analysis.
- Client-side data storage security assessment
- Authentication and session management testing
- Network communication security analysis
- Binary protection and reverse engineering resistanc
- Platform-specific vulnerability identification
API Security Testing
APIs are the backbone of modern applications but often contain security vulnerabilities that can expose sensitive data or functionality. Our API security testing service identifies these vulnerabilities through comprehensive manual testing.
- Authentication and authorization testing
- Parameter manipulation and injection testing
- Rate limiting and resource exhaustion checks
- Business logic flaw identification
- Sensitive data exposure assessment

Network & Infrastructure PenTesting
Our network and infrastructure PenTesting service identifies security vulnerabilities in your network architecture, servers, and infrastructure components. We follow MITRE ATT&CK, PTES, and OSTMM methodologies to provide comprehensive coverage.
- External and Internal network PenTesting
- Server configuration and hardening assessment
- Network device security evaluation
- Privilege escalation testing
- Lateral movement assessment
Red Teaming Exercises
Our Red Team exercises simulate sophisticated attacks to comprehensively test your organization’s security posture. Unlike traditional penetration testing, red teaming takes a goal-oriented approach to identify security weaknesses through the lens of determined adversaries.
- Black-box testing with minimal prior information
- Multi-vector attack simulation
- Objective-based security assessment
- Evasion technique testing
- Detection and response capability assessment

AI/LLM PenTesting
Our AI/LLM PenTesting service focuses on evaluating the security of AI and Large Language Model systems identifying logic flaws, data leakage, prompt injection risks, and model manipulation vulnerabilities. We test how secure your AI really is against modern adversarial techniques.
- Prompt injection and jailbreak attack simulation
- Model poisoning and data extraction testing
- Adversarial input and output manipulation
- Access control and API exposure assessment
- Secure model deployment and governance validation
IoT / ICS / SCADA PenTesting
Our specialized testing for IoT, Industrial Control Systems, and SCADA environments ensures resilience across connected devices and critical infrastructure without disrupting operations.
- Protocol-level and firmware analysis
- Network segmentation and access control validation
- Device and gateway vulnerability exploitation
- Safety-aware Red Team simulations
Vulnerability Assessment
Our vulnerability assessment service provides a comprehensive evaluation of your systems and applications to identify security vulnerabilities. We combine automated scanning with manual verification to deliver accurate results with minimal false positives.
- Comprehensive vulnerability scanning
- Manual verification of findings
- False positive elimination
- Risk-based prioritization
- Detailed remediation guidance
Managed Security Services
Our managed security services provide ongoing security monitoring, assessment, and support for your organization. We offer flexible engagement models to meet your specific security needs and budget constraints.
- Continuous vulnerability management
- Regular security assessments
- Security advisory and consultation
- Incident response support
- Security awareness training
PenTest-as-a-Service (PTaaS)
Our PenTest-as-a-Service offering transforms traditional penetration testing into a continuous, subscription-based model. This approach provides ongoing security coverage, real-time reporting, and seamless integration with your development environment.
- Continuous security testing coverage
- Faster vulnerability reporting
- Integration with development workflows
- Flexible testing schedules
- Access to our CrowdSpark platform
Ready to Secure Your Business?
Let our team of ethical hackers help you identify and address vulnerabilities before they can be exploited.
